In IoT “S” stands for security
(c) one smart guy in Twitter
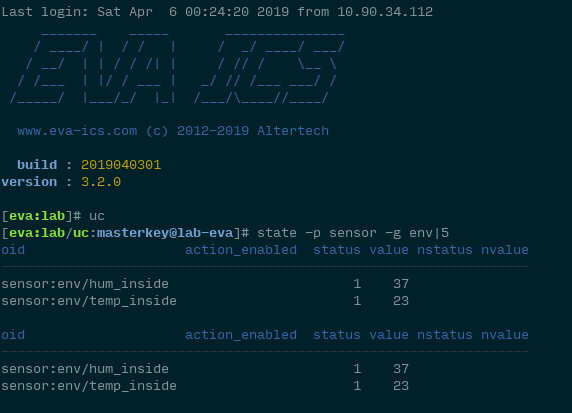
Weak security is a major problem of almost all modern IoT and IIoT/Industry 4.0 solutions. There’s usually nothing wrong when equipment state or shadow state is available for nodes in your configuration, as one of Industry 4.0 design principles is “Information transparency”.
However things change when we start talking about control. Allowing nodes to control each other and send action API calls is dangerous: if attacker get an access to information exchange point, he can destroy your business or even your life.
Continue reading “IoT and security”